
February 8, 2019
Free as in Freedom of Speech - Part 1 Mobile security threats and defenses
This miniseries of #HackForJournalism blogs introduces mobile security threats used against journalists and our solution for securing mobile as presented 4.2.2019 in Brussels. The goal of the #infosec Hackathon for Journalists event was to introduce journalists to mobile threats and share information on how to protect themselves. We know that currently used security tools are alone not enough so we invited journalists to co-design a truly secure mobile system from the ground up.
There is not much you can do to make your smartphone secure. Not because you don’t want to or don’t try to but because they were never developed to be secure. In the end our smartphones are controlled by manufacturers, companies and phone carriers, not to even mention about 3rd party applications and their data collecting. The only option we have, is to trust those in control not to misuse their power. We can only assume that manufacturers won’t put backdoors in their systems, that operators won’t sell our location data and that 3rd parties won’t sell our personal information to the highest bidder.
However, that is not the case. Thanks to the investigative journalists, whistleblowers, activists and researches, we have learned about cases where mobile malware vendors and governments use these vulnerabilities to target anyone considered as enemies. What makes these spyware programs so powerful is that they exploit the most integrated piece of technology in our lives – smartphones.
These very people who work hard to show us the side of events that we are not able to see ourselves, are the ones being targeted. And their lives may depend on their mobile security.
We need good journalism to defend freedom of speech, fight against anonymity and defend privacy. Journalism needs us to make secure, powerful and useful tools to be able to operate safely. We need each other.
We want to bring freedom in the mobile world. That being said, our job is to stay on top of mobile security issues. We found ourselves continuously encountering news and reports about journalists and activists being targeted and attacked. We started to further investigate this issue and as we gained more information about why these people were targeted, how they were spied on, and by who, there was no way for us not to do anything about it - especially when we have something to give out.
The most sophisticated spyware ever known
We were introduced to NSO Group’s Pegasus by the reports of the Citizen Lab back in 2016 and later by Lookout. Pegasus, like the other similar spyware programs, take advantage of undisclosed vulnerabilities found in iOS and Android. This is the part where the highly resourced players take the lead. These zero-days are actually so valuable, that some companies are offering millions of dollars to whoever is capable to find them. The duopoly of Android and iOS makes you an ‘easy target’ since you probably use one of the two. Even though you don’t know what is running on your device, doesn’t mean that others don’t. Once the malware like Pegasus is correctly installed (undetected by the target) it gets access to virtually everything in your smartphone.
Couple weeks ago, on January 30th, we learned, that Pegasus has a baby sister - Karma. We learned this from Reuters Investigates - who published two articles about it. According to the published report, Karma was developed by former U.S. government hackers on behalf of a foreign intelligence service United Arab Emirates, that spies on human rights activists, journalists and political rivals in a project called “Raven”. Some of the reported targets were Tawakkol Karman - face of the Yemeni uprising - part of the Arab spring in 2011.
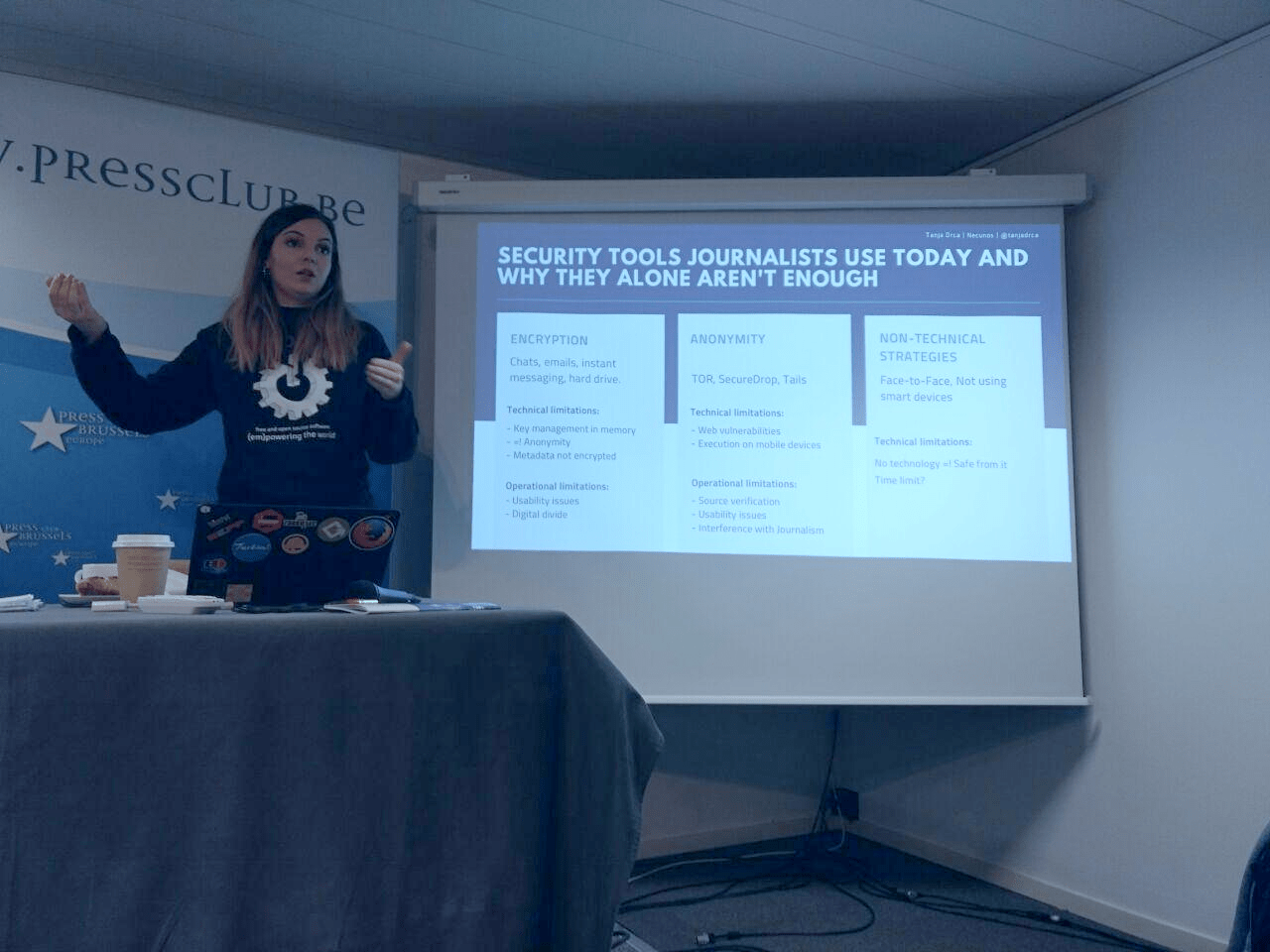
Mobile security tools journalists use today and why they alone are not enough
Journalists use various tools to secure communications between each other and their sources. Though valuable, like most of security and privacy tools have weaknesses which may not be recognized by the users. For example anonymous emails and chats may lack legal protections and encryption doesn’t cover metadata, which is not commonly known fact among reporters. https://www.usenix.org/node/190977. In order to develop a secure mobile ecosystem for journalists, we need to understand methods and functions which are important in their work. We need to analyze not only the good qualities of currently used tools, but the failures as well, in order to understand the factors that determine whether something created is going to be adopted and widely used.
Encryption is a critical component of information security. When used correctly, it comes to be nearly unbreakable. This becomes a problem for those who want access to the encrypted information. Targeting a system that is nearly unbreakable is not worth the time, effort or cost, so what to do? The answer is to bypass encryption using ‘backdoors’. The most vulnerable place for encrypted data is not during transit from place to place, but rather when it’s displayed at one end or the other – in this case, on a smartphone. It’s not about attacking the cryptography rather than finding a way to access the end point. Long list of applications that appear to provide end-to-end encryption fail to provide those guarantees when faced government requests. Major non-technical vulnerabilities are found to be linked to usability issues, which weaken the security. If the journalist finds use of non-automated encryption to be hard or anonymous file sharing interfering with the job, it may be left unused. Or rather, not used correctly.https://www.usenix.org/node/190977. Even if these anonymous file drops work as a great tool for some sources to journalists they are not as convenient, since the verification of the source is not possible. Communications between the journalist and source must be anonymous to everyone else but the journalist with whom they are communicating with.
Many journalists still may feel that the information they handle or possess is not relevant for anyone to attack over. This may be the case, but in addition to specific targeted surveillance, mass surveillance is perhaps even more effective in the eyes of the ‘attacker’. Mass surveillance means more data, more leaks and better known connections between journalists and their sources. It may not interest the attackers who you are as much as who you know and who you talk to. Even as a passive method, mass surveillance weakens the trust between sources and journalists.
We strongly suggest that everyone, especially journalists should use encryption to protect their data. In fact it is core value of our communications infrastructure. When it comes to the mobile information security, our solution is to provide encryption as a default in our NE_1 communication platform and to make it as usable as possible together with future end-users. To secure the weakest link - the endpoint, we suggest clean, auditable hardware - NE_1 mobile with free and open source necunOS operating system to exclude backdoor possibilities.
Creating secure mobile communication tools is a monumental task and cannot be achieved by any one company alone in the current mobile world. For this reason, we need and want to work together with communities, organizations and other companies to boost the development of free and open-source operating system alternatives to iOS and Android. The software alone is not enough though and that is why we are providing a new hardware built with open components.
In the next blog we will cover more currently used tools and methods in mobile security and discuss the possible solutions for securing mobile communications between journalists and their sources.