November 9, 2018
USB, the easy way in to a computer
We would like to take the time in this short blog post to discuss the USB port more and the potential threats surrounding it. We also go over potential solutions currently for USB based attacks and our choices for Necuno Mobile USB connectivity.
USB uses and threats
USB has been around for a long time and is now the bread and butter for mobile phone charging and data transfer for obvious reasons. It’s easy, versatile and universal. Usually security can be thought of a spectrum where ease of use is on the other end and high security on the other. So most of the time ease of use comes with a cost, less security. USB offers an easy way into a single machine and for that reason it is commonly used in highly targeted attacks against enterprises and individuals. Only downside in using USB for malicious attacks is that it needs a physical connection, which is exactly the reason why it is usually only used in very targeted attacks.
Obviously as USB ports exists in mobile devices, there are plenty of exploits created for them. Latest one that gathered fair amount of attention was the use of AT commands through USB that were available in most Android devices. These can be run on your device from any USB outlet that you plug your device into.
“We methodically tested our corpus of AT commands against eight Android devices from four different vendors through their USB interface and characterize the powerful functionality exposed, including the ability to rewrite device firmware, bypass Android security mechanisms, exfiltrate sensitive device information, perform screen unlocks, and inject touch events solely through the use of AT commands.”
These exploits are mostly prevalent in enterprise settings where hackers, state-backed or rogue groups, target businesses in order to infiltrate their networks, obtain sensitive data and is often used as an entry point in to systems, airgapped or not. (Airgapped systems are systems that are not connected to the internet thus only way into them are physical connections. Although some very clever solutions have been made to attack airgapped systems even without connection. But we wont get into them in this blog) This is why a lot of businesses with any kind of Operational Security forbid their employees from plugging anything into their USB ports. Its far more costly to do an incident response after the fact rather than practicing proper OpSec. Broader scope of targets can be attacked for example by offering free USB connected devices such as small USB devices as gifts or by providing a public USB charging station that runs exploits or gathers data when suitable mobile devices are connected to it. Bleeping Computer has gathered a nice set of USB related exploits and malware
Solutions
There can be preventions on software side that blocks the USB data exchange until user accepts or interacts with it. These do not block everything though, connected USB will exchange some information with the machine for example when you connect your device with your computer through USB, the device and computer will do a handshake where some information is exchanged about the connected device. Or as was the case with the earlier referred AT commands on some Android devices the AT command interface was exposed even without USB debugging enabled.
There are more robust solutions in protecting infiltrations through USB ports like the USB condom for example. It disables the data exchange completely and only allows charging through the USB. This is often recommended in case you need to plug random phones in to your computer.
Our choices
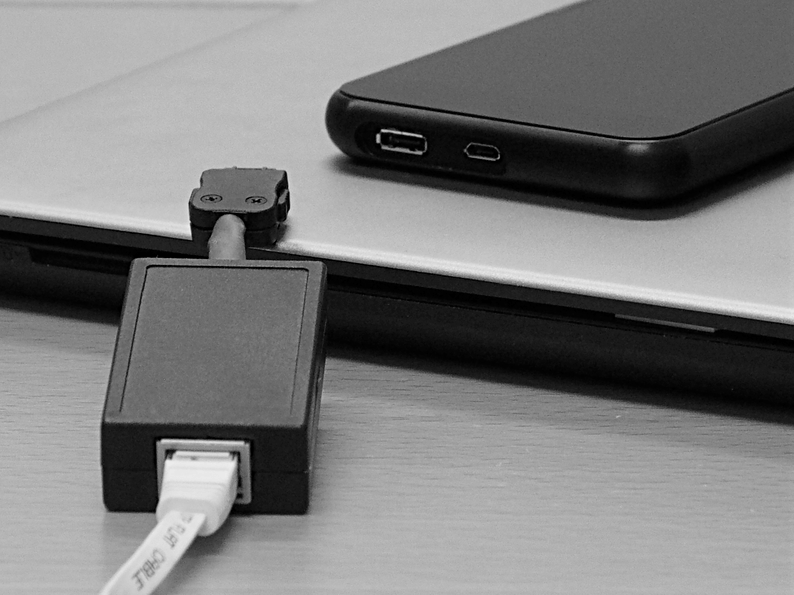
Our solution with the first iteration of Necuno Mobile was to get rid of the data pins completely to protect from any kind of USB attacks. Your Necuno Mobile will be completely safe from USB hacking. Connections to the phone happen through WiFi or directly through the Ethernet port. For the engineering people there is a possibility of using the serial port. There have been controversial reports of border officers at certain airports infiltrating phones through USB and installing software on it. Our solution completely mitigates this and device can safely be used for international travel.
Contact us through our email if you have any questions or comments contact@necunos.com. Make sure to follow us on twitter and subscribe to our newsletter and we’ll keep you updated on our progress.